A new Android malware pretends to update Google Chrome
It is obvious that a reliable application update does not brings malwares, but unfortunately, there are malwares that pretend to be app updates to those who do not fully know Android and mobile world in general.
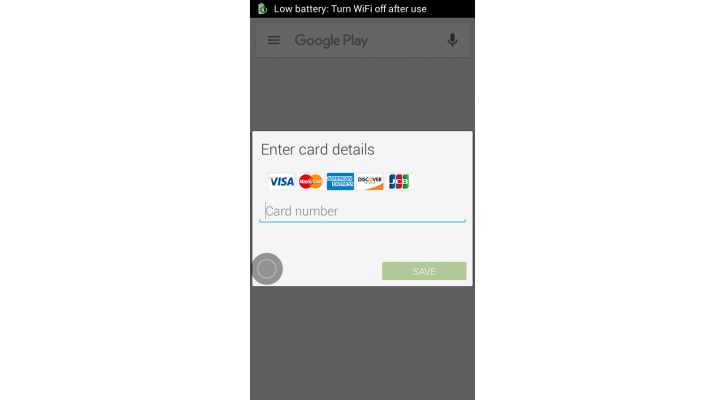
Zscaler (researchers involved in the world of computer security) has found circulating on the internet a fake update for Google Chrome and distributed via .apk, uploaded to domains containing the words Google/Android/Google Chrome, which once installed and run requires Administrator privileges (root). Later, this malware checks for antivirus programs, monitors internet browsing, calls and SMS but, above all, try to get the credentials of the user’s credit card via pop-up very similar to an official update.
According to Zscaler, the only effective method to remove malware would be doing a factory reset in the device. Of course it is obvious that if Chrome needs to be updated will be done automatically directly from the Google Play Store, but there are many inexperienced users who could easily fall into this trap, then the recommendation is as follows: if you are surfing in and out notifications update for Google Chrome to download, avoid it and forget it.
Unfortunately, we do not know how it spreads and how this new Android malware comes, as Zscaler added nothing about this, but argued that use temporary URL and the malware and the source from whence it came is not easy to identify. Actually, it’s not easy that this new Android malware takes possession of our device, in fact we have to be still us to grant admin rights once we have downloaded, so we should commit two consecutive errors to give access to our device.
This new Android malware is able to: steal the call data, close calls, automatically uninstall antivirus and apps already installed on your device, steal messages, stealing the data of your credit card from the Play Store (as a data confirmation popup dumps on the phone, similar to that of Google, but then sends this data to an external server and not to Google), steal other sensitive corporate information stored on your smartphone. In case of infection, proceed as soon as possible to reset to factory data, as it is the only way to remove it.
