Drive-by attack is used to install ransomware on Android
The experts at Blue Coat Labs have sounded the alarm: a group of computer criminals would force the installation of ransomware on older Android devices not updated and still today used by millions of people around the world.
Usually, the Android malware infects the device after downloading and the actual installation of an APK file. What we will discuss is a decidedly atypical malware and acts independently when you visit a particular web site. Unfortunately it was not revealed what the offending web site is, but usually, this type of malware are spread on pornographic sites. Exploiting some known vulnerabilities present on older Android versions, the malware will auto-install on the device and acts like any other ransomware: calling for a “ransom” in exchange for malware removal or sending your sensitive data.
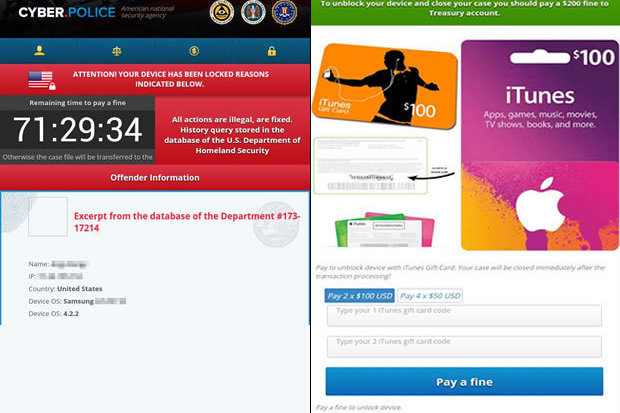
In this case, the ransomware claims payment in gift cards for iTunes. The problem is not with the latest smartphones. In fact, according to the statement from Blue Coat Systems, malware acts only on devices with Android 4.0 version through 4.3. However, it seems that even devices running Android 4.4 are exposed, albeit to a lesser extent. Fortunately, it only needs a common Restoring factory settings to remove malware.
In fact, what we have described is just one of hundreds of malware circulating on the Internet every day. The best way to avoid running into this kind of “virus” is to update the firmware of your device whenever the opportunity presents itself. Another good advice is to stay away from unsavory web sites.
Ransomware installed on the vulnerable device does not encrypt the content, but displays a fake message warning by referring to the detection of alleged illegal activities. The user is then invited to pay a penalty in order to obtain the release of the device. To avoid taking risks, once again, the suggestion is to update to the latest version of Android. Many manufacturers, in fact, unfortunately, do not release official updates for older Google operating system or otherwise for medium to low-end devices.
